So I got an interesting email from Google this evening:
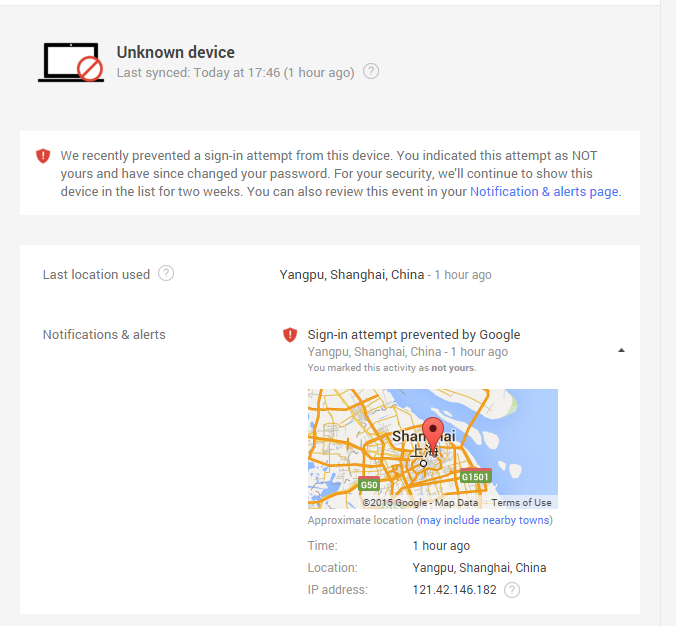
The attacker had my password and my gmail account name. The only reason they didn’t get into my account, I think, is because I use two-factor authentication that requires me to input a randomly generated number from the Google authentication app that resides on my phone before it will complete the authentication process and allow full access.
The worrying thing for me was wondering how my password was compromised. I actually put some brain cells behind the process and realized I gotten incredibly lazy in my choice of password since I’d activated two factor. My password was 8 characters consisting of 6 alphas and 2 numbers and three different permutations that I rotate through over the course of a year. I’ve since changed that password, and any others that used such a simple algo and changed it to something I use on other sites which consists of four words that mean absolutely nothing when put together, equal 25 characters in length and are easily remembered.
Still concerned, I visited BreachAlarm.com and discovered that there was a data breach at Xsplit.com back in 2013 and some of that data was only brought to light on the 25th of October of this year. No coincidence that a month later, my email account is being prodded with the hope of taking it over.
The cool thing about most web-based accounts these days (I’ll add that this is in my experience) allow for the main email attached to an account will be notified in the event of a change in account information. Because of this, the attacker really wants to take over the contact email account so they can control the information reaching the target before the attacker’s actions have reached completion.
So I’ll just put this one here, again, for the use of people who may be of the mind that your password needs to be hard to remember. Your password doesn’t need to be complex; just needs to be difficult to guess.

